Introduction
Traditional cybersecurity models are no longer sufficient to defend against sophisticated cyber threats. Enter Zero Trust Architecture (ZTA)—a security model designed for a world without boundaries. In ZTA, no user or device is trusted by default, even if they’re inside the network perimeter.
What is Zero Trust Architecture?
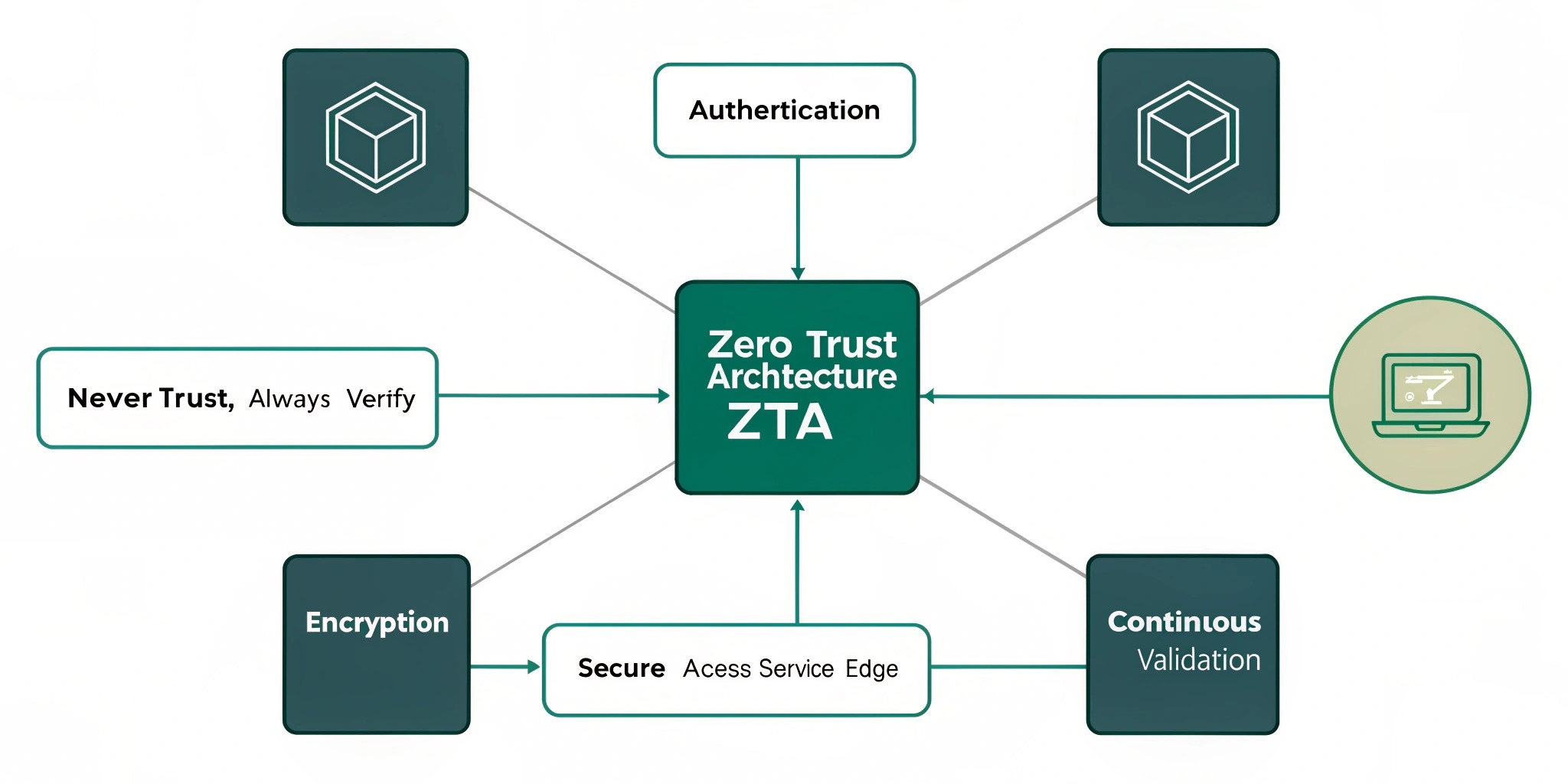
Zero Trust is a security framework that requires continuous verification of user identity and device health before granting access to resources. Unlike perimeter-based models, ZTA assumes that threats can come from both outside and inside the network.
Core Principles of Zero Trust
- Verify Explicitly – Authenticate and authorize based on all available data points.
- Use Least Privilege Access – Limit user access rights to the minimum necessary.
- Assume Breach – Design systems assuming attackers are already present.
Key Components of ZTA
- Identity and Access Management (IAM)
- Multi-Factor Authentication (MFA)
- Microsegmentation
- Device Compliance Verification
- Real-Time Monitoring and Analytics
Benefits of ZTA
- Enhanced protection against ransomware and insider threats
- Improved regulatory compliance (GDPR, HIPAA, etc.)
- Supports remote and hybrid work environments
- Reduces attack surface by minimizing unnecessary access
ZTA Use Cases
- Securing remote employee access
- Protecting sensitive government data
- Enhancing cloud infrastructure security
- IoT and device management
Challenges in Implementation
While ZTA improves security posture, it also brings challenges like:
- Complexity in integration with legacy systems
- Increased demand for identity governance
- Need for a cultural shift in cybersecurity thinking
How to Start Your ZTA Journey
- Assess current security posture.
- Implement strong IAM and MFA.
- Start with microsegmentation of sensitive resources.
- Adopt a phased approach to implementation.
Conclusion
Zero Trust is not a product—it’s a mindset. As cyber threats continue to evolve, organizations must adopt Zero Trust principles to future-proof their security infrastructure. It's time to eliminate implicit trust and build a resilient, secure digital foundation.